HTB Writeup - WingData
An easy rated Linux machine running an FTP webapp
February 19, 2026
Intro
Whoops, just realized I missed the first two week of the HTB season. Week 3 is WingData, an easy rated Linux box. The server is running OpenSSH and a webserver that takes you to a page for a file sharing program.
Clicking “Client Portal” takes you to ftp.wingdata.htb, a login page for Wing FTP Server.
Initial Intrusion
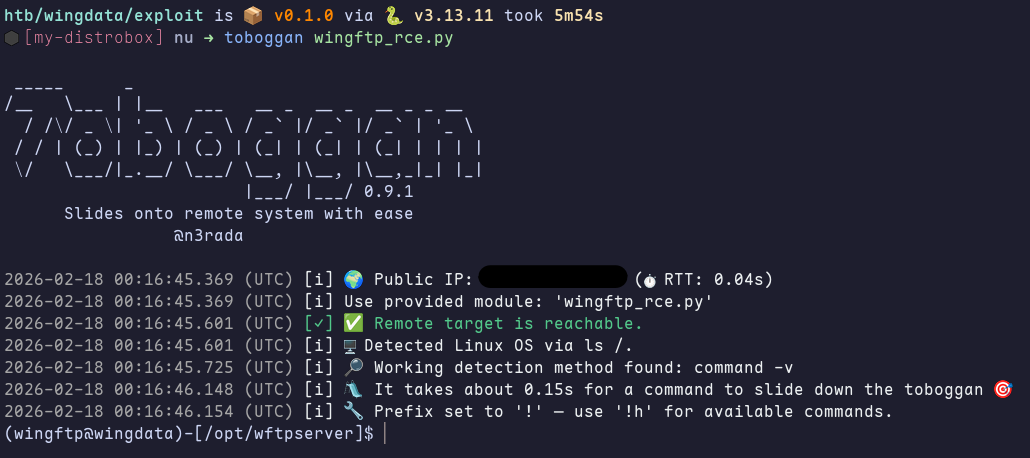
The initial intrusion here is very simple to find and execute. The version of Wing FTP Server is displayed as v7.4.3, and a quick search finds a critical CVE for it. The vulnerability is caused by improper handling of null bytes in the username value. A maliciously crafted request can inject Lua code into session files, which can then be executed by visiting the targeted path.
I wrote a custom RCE module to use with toboggan, giving me a more convenient to use shell. One small issue I ran into was that my script didn’t log out after, which eventually lead to me hitting the log on limit for the user anonymous. After adding a request to the logout endpoint to my module and restarting the server, I had a nice simple shell.
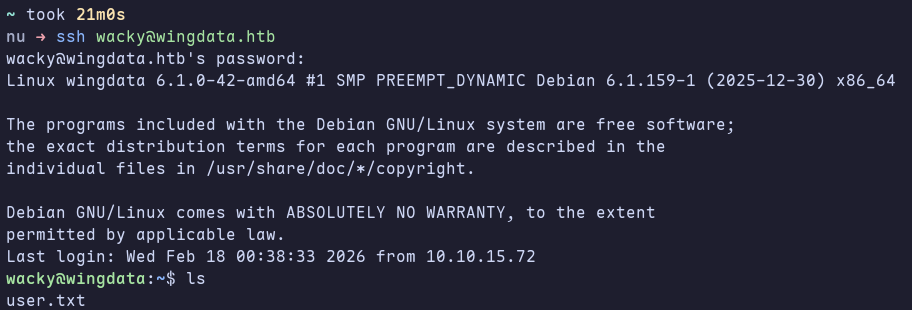
After looking around on the system for a bit I found a user named wacky who had a Wing FTP account and a local user. The file /opt/wftpserver/Data/1/users/wacky.xml contained account data, including the hash. After some research about how Wing FTP hashes passwords, I found that it was a SHA256 hash with the salt string “WingFTP” appended. With this info, I was able to crack the password using hashcat and rockyou.txt, allowing me to ssh into the system as wacky and giving me flag.
Privilege Escalation
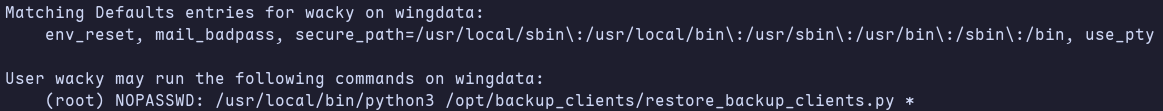
The first thing I checked for was wacky’s sudo priviledges with sudo -l, where I found that wacky is allowed to run a python backup script with any input.
I took a look at the script to see what could be exploited. The use of tarfile stuck out the most, and I quickly remembered hearing about a critical CVE from last year. This was CVE-2025-4517, which can be used to perform arbitrary filesystem writes. With a little more searching, I found this particularly handy exploit that includes preset attacks for priviledge escalation, including one that injects an SSH key into /root/.ssh/authorized_keys.
To exploit the vulnerability, all I had to do was generate a malicious tar archive using the exploit, then run the backup script on it.
I even started the machine up again to go redo the exploit for > screenshots, but I suddenly can’t even ping it.
All that was left was SSHing in as root and grabbing the key.